 In my previous blog post, I explained my concern that if we as a society don’t take digital privacy seriously, we will probably head into dangerous directions. Over the last few months, I have experimented with different tools and formed strategies to enhance my personal privacy and to start steering society in a positive direction. The journey so far hasn’t been easy, it required me to dig under the surface of the world wide web and to become more tech savvy than I anticipated. With this blog post, I want to give you guidance in taking digital privacy seriously.
In my previous blog post, I explained my concern that if we as a society don’t take digital privacy seriously, we will probably head into dangerous directions. Over the last few months, I have experimented with different tools and formed strategies to enhance my personal privacy and to start steering society in a positive direction. The journey so far hasn’t been easy, it required me to dig under the surface of the world wide web and to become more tech savvy than I anticipated. With this blog post, I want to give you guidance in taking digital privacy seriously.
A rule of thumb to keep in mind is that privacy, usability and low cost never co-exist.
- If you want easy to use tools for free; Google, Facebook, etc. are your options. But remember you’ll pay by giving your privacy away.
- If you want easy to use tools that respect your privacy, just like the service of your regular phone provider, it will cost you some money.
- If you want tools that respect your privacy and are free to use, open source tools are the option, but they are a bit tricky to use.
Carry very strong keys
Just like you have a key to safeguard the privacy of your house, you use a key for shielding your online home from intrusion. But the problem with your online home is that it has many doors to enter and it’s hard to remember all those login details. It’s likely you’ll only use one username and password for all your digital access and maybe that’s your Google or Facebook login. Whoever gets hold of your login details can enter your private content, from anywhere in the world. And because your ‘online facade’ is displayed all over the word, anyone can guess multiple entrances to your online home. When you only carry a one size fits all username and password, you are an easy target for identity theft.
An additional problem with Google or Facebook logins is that these companies track your online activity to feed their algorithms. The longer you stay logged in, the more they can track your behaviour and the bigger your ‘echo chamber’ (see my previous blog post) will become. Ideally, you should log-out straight after you visited Gmail or Facebook, so the tracking would be limited.
As the first step in taking privacy seriously, I strongly recommend you to start using a password manager. This is a software that remembers all your login details for you. You can create a unique password for every login you own. You only have to remember one master password to start the software and it will pull up your unique password for a specific website. In addition, the password manager can create extremely difficult unique passwords for you so it becomes visually impossible to crack your login details. A password manager is also recommended if you often log into your accounts from public spaces. Someone peeking over your shoulder will only be able to spy the master-key to your manager and not to the unique password for a particular website.
Encrypt your footprint
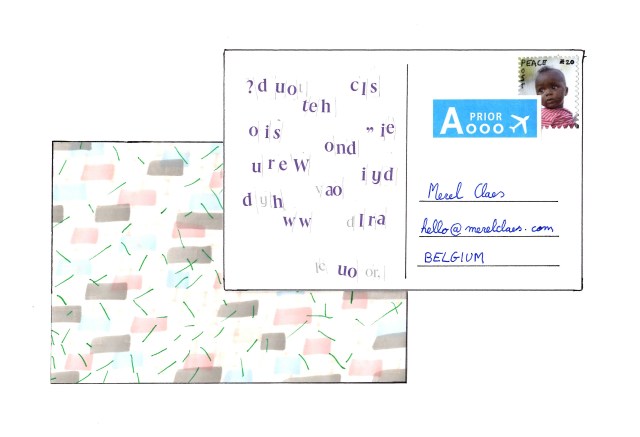
You wouldn’t like it when your postman reads your correspondence before putting it in your letterbox, right? That is why we use sealed envelopes! What we don’t realise is that a lot of the information we send via the internet has no seal on it. The internet has many ‘postman’ and they often take exotic, instead of direct, routes. So you don’t really know which corporation or government reads your correspondence along the way. Encryption converts your correspondence with a key. It’s unreadable when you don’t know the converter key. So when you send encrypted data, it will be meaningless chunks of data for many. It’s like sending holiday cards with on one side only coloured stains and on the other side random letters, an address and a stamp. The postman will deliver it to the right place, but no-one in the chain will have a clue of what is communicated.
Free email providers like Gmail do encrypted email, but not on their servers. Data on their servers remain meaningful so they can create personalised advertising. End-to-end encryption allows that your data is only readable on de devices of the end users, and nowhere in between.
Pretty Good Privacy (PGP) is a way to send an end-to-end encrypted email. It works as follow: A wants to send B an encrypted email. A looks up the public key of B and encrypts the email with this key. When it arrives in B’s inbox it is still encrypted, only B’s private key can decrepit the message. Signal is a mobile app that allows end-to-end encryption instant messaging. It is slightly more advanced in secure communication compared to tools like WhatsApp.
Diffuse your trail
When you use the internet, you follow certain routes and your digital footprints creates trails. These trails can be traced back to your device. Clusters of trails, especially from unencrypted content, are valuable for corporations and governments to label your behaviour patterns. This practice can trap people in echo chambers or can even be used to frame someone as a wrongdoer.
With a VPN connection to a proxy server, you can confuse the prying eyes of the internet by pretending you are someone else. The VPN connection acts like a tunnel trough the internet from your computer to another one. This other computer, the proxy server, will be the starting point for the digital trail of your surfing behaviour. There are VPN services available on the internet but keep the rule of thumb in mind. The proxy server will handle all your traffic while connected and could keep track of this. So you have to trust the proxy not to sell your privacy.
TOR is a browser that enables you to stay anonymous on the internet. It’s a combination of encryption and VPN. Your data travels via multiple VPN tunnels and at the end of every tunnel, it gets re-encrypted. Just like an onion, it takes many layers to get to the core. And the prying eye’s of the internet don’t like these onions because they are extremely hard or even impossible to decrypt the data or trace it back the source. The browser is freely available but having to go trough multiple layers will leave you with a slower browsing experience than you are used to.
Keys, encryption and diffusion are my top strategies to raise the standard of online privacy. It’s a new field for me and although my steps are tiny, I believe they are an important starting point. Maybe I have inspired you to also start taking privacy seriously. Or maybe you can help me going further. I am keen to hear from you! In my next blog post, I will go more practical in taking privacy seriously by sum up many concrete tips and tricks.